Saturday
Types of Cloud Computing

- Public Cloud : A public cloud
can be accessed by any subscriber with an internet connection and access to the cloud space.
- Private Cloud: A private cloud
is established for a specific group or organization and limits access to just that group.
- Community Cloud : A Community cloud is shared among two or more organizations that have similar cloud requirements.
- Hybrid Cloud : A hybrid
cloud
is essentially a combination of at least two clouds, where the clouds included are a mixture of public ,private or community.
What is Cloud(Computing) ?
Friday
What is Cloud(Computing) ?

so, Like Emails when you want to access your emails you open your web browser. go to the email client and log in. The most important part of the equation is internet access. no like your physical computer where software installed.
You can use it anywhere .so this is how cloud computing work.little diff instead of accessing just email , you can choose what information you have to access to within the cloud.
Thursday
How to install Telnet in windows 7?
By default, Telnet is not installed with windows , you can install with following steps
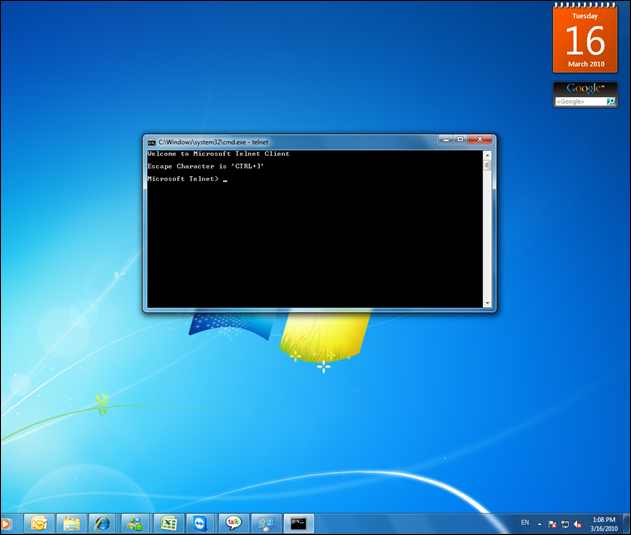
- Go to Control Panel and Then Click Programs.
- Under Programs and Features, Click Turn Windows Features On or Off, If you are prompted for an administrator password or confirmation, type the password or proved confirmation.
- In the Windows Features Dialog Box , Select The Telnet Client Check Box.
- Click OK, the installation might take several Minutes.
Wednesday
what is http://
The Hypertext Transfer Protocol(HTTP) is an application protocol for distributed, collaborative,hypermedia information systems.
HTTP is the foundation of data communication for the world wide web.
HTTP functions as a request response protocol in the client server computing model.
In HTTP a browser an example acts as a client, while an application running on a computer hosting a website functions as a server. The client submits an HTTP request message to the server. The server which stores content, or provide resources, such as HTML files, or performs other functions on behalf of the client. returns a response message to the client.
The HTTP protocol is designed to permit intermediate network elements to improve or enable communication between clients and server.
HTTP is an application layer protocol designed within the framework of the internet protocol suite.
More about how Internet work
Tuesday
Window 7 revealed The hidden Truth
How To use hidden International Wallpaper and themes
- In the search box Or RUN , type C:\windows\Globalization\MCT and press Enter (if your windows is installed in C Drive else D,E,F whatever).
- Will show you a list of subfolder like MCT-AU,MCT-CA, MCT-GB etc Each folder has wallpaper for a specific Country.
- For any of the countries whose wallpaper and themes you want to use , then go into its theme folder and click on
- That will install shortcut to the theme and wallpaper in the personalization section of control panel.
Power Efficiency Report in Windows7
How to improve Battery life in laptop
- Run a command prompt as an administrator . To do this Type CMD in the search box and when cmd icon appears, right click it and choose “ run as administrator “.
- Command line Type “ powercfg –energy –output \folder\energy_report.html
Where folder = you want the report to be placed.
after a minute windows 7 will examine the behavior of your laptop. and you will get a report .
follow its recommendations for ways to improve power performance.
How To Run Xp Software in Windows 7
If you have Important software that no longer runs under windows7 Then you Can Use Xp Mode.
A virtual copy of Xp that runs in a window on your windows 7 Desktop.
But Problems is as a Xp mode only works with the system that have Hardware Virtualization (AMD Or Intel VT) Built in and turned on.
If you have Compatible CPU then this may just be matter of enabling the option in your BIOS set up program.
In some high profile Brands (Sony vaio,) Disable the setting for security reasons. and that blocks XP mode from working too.
one solution but It’s little risky as essentially you will have to alter a byte in you laptop firmware and hope this doesn’t have any unexpected side effects.
Don’t blame on me if wrong.
Monday
What is Windows Error Reporting ?
Windows error reporting collects and offers to send post error debug information, using the internet, to the developer of an application that crashes or stops reporting on a user’s desktop. No data is sent without user confirmation.
When a error signature information reaches the Microsoft server ,its is analyzed ant a solution is sent back to the user when one is available.
If windows error reporting itshelf crashes, then an error reports that the original crashed process cannot be sent.

You can view some of Error code (Click) System Error Code
Sunday
Intel Turbo Boost Technology
Intel Turbo boost Technology Provide even more performance when needed on 2nd generation Intel Core processor .
Intel Turbo boost Technology 2.0 is activated when the operating system requests the highest processor performance state P0.
Intel Turbo boost technology depends on the workload and operating environment.(Depend on the number of active cores).
Workload :
- Number of active cores
- Estimate current Consumption.
- Estimate Power consumption.
- Processor Temperature.
when the processor is operating below these limits and the user’s workloads additional performance, the processer frequency will dynamically increase until the upper limit of frequency is reached.
Intel Turbo boost can parallel manage current, power and temperature to maximize performance and energy efficiency.
Source : Intel Turbo boost page
Monday
How to Bypass BIOS Passwords
How to Bypass BIOS Passwords
BIOS passwords can add an extra layer of security for desktop and laptop computers. They are used to either prevent a user from changing the BIOS settings or to prevent the PC from booting without a password. Unfortunately, BIOS
 |
| What is BIOS |
DISCLAIMER
Please remember that most BIOS passwords do not protect the hard drive, so if you need to recover the data, simply remove the hard drive and install it in an identical system, or configure it as a slave drive in an existing system. The exception to this are laptops, especially IBM Thinkpads, which silently lock the hard drive if the supervisor password is enabled. If the supervisor password is reset without resetting the and hard drive as well, you will be unable to access the data on the drive.
 |
| Bios Password Page |
Backdoor passwords
Many BIOS manufacturers have provided backdoor passwords that can be used to access the BIOS setup in the event you have lost your password. These passwords are case sensitive, so you may wish to try a variety of combinations. Keep in mind that the key associated to "_" in the US keyboard corresponds to "?" in some European keyboards. Laptops typically have better BIOS security than desktop systems, and we are not aware of any backdoor passwords that will work with name brand laptops.
WARNING: Some BIOS configurations will lock you out of the system completely if you type in an incorrect password more than 3 times. Read your manufacturers documentation for the BIOS setting before you begin typing in passwords
BIOS backdoor passwords:
AMI BIOS backdoor passwords:
Manufacturer Password
VOBIS & IBM merlin
Dell Dell
Biostar Biostar
Compaq Compaq
Enox xo11nE
Epox central
Freetech Posterie
IWill iwill
Jetway spooml
Packard Bell bell9
QDI QDI
Siemens SKY_FOX
TMC BIGO
Toshiba Toshiba
TOSHIBA BIOS
Most Toshiba laptops and some desktop systems will bypass the BIOS password if the left shift key is held down during boot
IBM APTIVA BIOS
Press both mouse buttons repeatedly during the boot
Password cracking software
The following software can be used to either crack or reset the BIOS on many chipsets. If your PC is locked with a BIOS administrator password that will not allow access to the floppy drive, these utilities may not work. Also, since these utilities do not come from the manufacturer, use them cautiously and at your own risk.
Cmos password recovery tools 3.1
!BIOS (get the how-to article)
RemPass
KILLCMOS
Using the Motherboard
Many motherboards feature a set of jumpers or dipswitches that will clear the CMOS and wipe all of the custom settings including BIOS passwords. The locations of these jumpers / dipswitches will vary depending on the motherboard manufacturer and ideally you should always refer to the motherboard or computer manufacturers documentation. If the documentation is unavailable, the jumpers/dipswitches can sometimes be found along the edge of the motherboard, next to the CMOS battery, or near the processor. Some manufacturers may label the jumper / dipswitch CLEAR - CLEAR CMOS - CLR - CLRPWD - PASSWD - PASSWORD - PWD. On laptop computers, the dipswitches are usually found under the keyboard or within a compartment at the bottom of the laptop.
Please remember to unplug your PC and use a grounding strip before reaching into your PC and touching the motherboard. Once you locate and rest the jumper switches, turn the computer on and check if the password has been cleared. If it has, turn the computer off and return the jumpers or dipswitches to its original position.
Removing the CMOS Battery
The CMOS settings on most systems are buffered by a small battery that is attached to the motherboard. (It looks like a small watch battery). If you unplug the PC and remove the battery for 10-15 minutes, the CMOS may reset itself and the password should be blank. (Along with any other machine specific settings, so be sure you are familiar with manually reconfiguring the BIOS settings before you do this.) Some manufacturers backup the power to the CMOS chipset by using a capacitor, so if your first attempt fails, leave the battery out (with the system unplugged) for at least 24 hours. Some batteries are actually soldered onto the motherboard making this task more difficult. Unsoldering the battery incorrectly may damage your motherboard and other components, so please don't attempt this if you are inexperienced. Another option may be to remove the CMOS chip from the motherboard for a period of time.
Note: Removing the battery to reset the CMOS will not work for all PC's, and almost all of the newer laptops store their BIOS passwords in a manner which does not require continuous power, so removing the CMOS battery may not work at all. IBM Thinkpad laptops lock the hard drive as well as the BIOS when the supervisor password is set. If you reset the BIOS password, but cannot reset the hard drive password, you may not be able to access the drive and it will remain locked, even if you place it in a new laptop. IBM Thinkpads have special jumper switches on the motherboard, and these should be used to reset the system.
| Intel Mother Board DP55SB |
Overloading the Keyboard
On some older computer systems, you can force the CMOS to enter its setup screen on boot by overloading the keyboard buffer. This can be done by booting with the keyboard or mouse unattached to the systems, or on some systems by hitting the ESC key over 100 times in rapid succession.
Jumping the Solder Beads on the CMOS
It is also possible to reset the CMOS by connecting or "jumping" specific solder beads on the chipset. There are too many chipsets to do a breakdown of which points to jump on individual chipsets, and the location of these solder beads can vary by manufacturer, so please check your computer and motherboard documentation for details. This technique is not recommended for the inexperienced and should be only be used as a "last ditch" effort.
| Intel Socket 1156 |
Thursday
Intel Original And Chipset Motherboard
A chipset usually contains several controllers that govern how information travels between the processor and other components.
so ,if we think we can

An original motherboard the entire product is manufactured by Intel. the circuit board and the IC’s which are on it.
Which one is better Intel original or Chipset motherboard ?
and chip set ‘it means some other company (mercury,asuas, D-link etc ) has designed and made the circuit board but has used the chipset provided by INTEL.

buying a chipset board is always compromise. some are good but..third party .
In an original motherboard entire products is manufactured by INTEL.Everything.
Intel original and chipset .in Intel chipset Intel makes only PCB and BIOS of the motherboard and gives to SYS,VIA or etc. vendors.
While Intel Original boards are prepared in Intel company will all other accessories
Systemctc Links More About
Tuesday
Useful Dos Commands
COPY Make a copy of file or Merge files together.
COPY original file DESTINATION FILE
where original file and destination file are file name separated by a space.
The command can be used to merge several file into one file like
COPY nj1 + nj2 systemctc
would copy nj1 and nj2 into systemctc
Note : file names used in the command must include the file extension if it exists. so if you were copying a nj.doc you need to include .doc extension in the filename.
DEL : Delete file
DEL filename
Where filename is the name of the file to be deleted.
DIR : Obtain a list of the files stored in a directory
if used without options this command will give a list of files in the current directory.including any extension and size.
if used with the option /P
as DIR /p
the same information will be displayed a page by page with the message.
if DIR/w
the listing is of names and extensions only and in a more compact format across the page.
DISKCOPY Take a security copy of your working disk
more here Free Download
Sunday
Linux ?
Operating system is what makes the hardware work together with the software.
Linux gives you a graphical interface that makes it easy to use your computer, It is only the Kernel that is named LINUX,The rest of the OS are GNU tools. some Variants Distribution Mandrake,SUSE Linux,Gentoo and Redhat .
Linux is made with one thought in mind Everything is a File.
A file is an element of data storage in a file system .File usually stored in hard drives,CD-ROMs and other media. but may also be stored in RAM or links to devices.

Organizing Our files into a system we use Folders. The lowest Possible folder is Root/ where you will find the user homes called /home/
let
/
/home/
/home/nj/
home/pj/
home/dj/
etc.
Files system Lowest folder root/ contains the following folders.
Systemctc Top of Town Now
Secure Computer: How to Bypass BIOS Passwords
Secure Computer: JTAG(Joint Test Action Group)
Secure Computer: Zero Insertion Force (ZIF)
Secure Computer: Hardware Programing ?
Secure Computer: What is Difference Between Bluetooth And NFC
Secure Computer: Windows RegistrySecure Computer: Shell
Secure Computer: Avoiding Virus Infections
Friday
JTAG(Joint Test Action Group)
Except for some of the very lowest end systems, essentially all embedded systems platforms have a JITAG support port in circuit debugging and firmware programming as well as boundary scan testing.
Zero Insertion Force (ZIF)
Its used in the design of IC Sockets and electrical connectors invented to avoid problems caused by applying force upon insertion and extraction.
A normal integrated circuits requires the IC to be pushed into sprung contacts which then grip friction.
Hardware Programming

Hardware Programing ?
For programing a circuit,its is either inserted into a socket often called ZIF. or programmers is directly connected by an adapter to the circuit board. afterward the data is transferred into the circuit by applying signals to the connecting pins.
Some circuits have a serial interface for receiving the programming data called JTAG .other require the data on parallel pins. by a programming pulse with a higher voltage for programming the data into the circuit.
Hardware programing language are
I know some of the are
C/C++
Java
ABEL
AHDL
BLUSPEC
ELLA
HML
HYDRA
LAVA
LOLA
And many more
Tuesday
DSL
Its main advantages over POTS is that it is much faster than analog modems, and it provides a permanent connection.
It allow you to make and receive regular telephone calls while you are connected to the internet.
Its main disadvantages is that its availability is limited by your proximity to the telephone company’s switching equipment.
DSL
IRC(Internet Relay Chat)
You All Are Familiar with The chat Rooms used by certain online Services.IRC is just like a chat room.
Thursday
What is Difference Between Bluetooth And NFC
- NFC and Bluetooth and NFC are both short range communication technologies
- NFC operate at slower speed than Bluetooth but consumes far less power and doesn’t require pairing.
- NFC sets up faster than standard Bluetooth.But is not faster than Bluetooth low energy.
- With NFC Two devices connect automatically.Less than a ten’s of second.
- Data Transfer rate (424 Kbit/s) slower than Bluetooth V2.1(2.1 Mbit/s) with maximum data transfer of less than 20 cm.
- NFC has short range (sometime its user becomes difficult in crowded areas)
What is NFC ?
lalalaaa ETC
Difference Between NFC and Bluetooth
What is NFC ?
NFC (Near Field Communication ) Allows for simplified Transactions,Data Exchange and wireless Connections Between Two Devices in proximity to each other,But not more than Few Centimeter.
- Tab one NFC Device to another to instantly share a contact,photo,songs, etc.
- Tap one NFC device to another to instantly share Electronic business cards or resumes
- To pay a friend, your could tap the devices and enter the amount of the payment.
- You can play a game with another NFC device(multiplayer game).
NFC can be used to high-speed wireless connection for expanded content sharing.
- Instant Bluetooth Pairing can save searching, waiting and entering codes,Touch the NFC devices togher for instant pairing.
- instant Wi-Fi configuration can configure a device to a wifi network automatically .Just Tap a NFC device to an NFC Enabled router.
What more NFC Can do ?
- Mobile Payment
- PayPal
- Ticketing
- Boarding Pass.
- Point of sale
- Coupons
- Tour Guide.
- ID Cards.
- Keycard.
- Rental Car and Hotel Keys.
ETC.
Hard Drive and Storage Media
Hard Drive and Storage Media
This is where a majority of the Information that the computer requires to operate is stored.Operating System Resides here.along with application such as word processor and games. This is also where significant amounts of data is stored.
so , though the use of temporary files and caches allows a forensic examiner to reconstruct the actions that a computer user has carried out on a computer, which files have been accessed an much more.
The file system Partitions,directories and individual pieces of paper(files) can be hidden and can easily be overcome.
above article must be long ! , but security reason lalalllb .. ok Search on any search engine you will find more interesting technique for dot otod .
Computer File Extension
What is Ethical Hacking ?
Nowadays , companies are hiring services from “Ethical Hackers'” to detect vulnerabilities of their computer science system and therefore,improve their defense measures.
Ethical Hackers, with their knowledge, help to define the parameters of defense. They do “controlled” attacks, previsousl authorized by the organization, to verify the system’s defenses.They create groups to learn new attacks techniques, exploitations and vulnerabilities, among others, they work as researchers for the security field.
The Methodology of ethical hacking is divided in several phases
- Attack Planning
- Internet Access
- Test and Execution of an attack
- Gathering information.
- Analysis
- Assessment and Diagnosis
- Final Report
Ethical hackers,
How to Secure Computer
How firewall Protect Your Computer
System Crash
How The Web Really Works ?
Assuming you are already connected to the internet , Here are the steps that occur in order
How web Work steps
- You Open Your Browser.
- You type in the URL(website name).
- Website name saved in History Cache on the Hard disk.
- Your computer looks up the name of the address to your default DNS server to find the IP address.
- Your Computer connects to the server at the IP address provided ate the default web port of 80 TCP if you used “HTTP://” or 443 TCP if you used “ HTTPS://” at the front of the web server name.(‘HTTPS’ steps not follow in this example )
- Your computer requests the page or directory you specified with the default often being “index.htm” if you don’t specify anything.But the server decide its default and not your browser.
- The pages are stored in a cache on your hardisk. Even if you tell it to store the information in memory(RAM), there is a good chance it will end up somewhere on your disk either in a PAGEFILE or in a SWAPFILE.
- The browser nearly instantaneously shows you what it has stored. Again, there is a difference between “perceived speed” and “actual speed” of your web surfing which is actually the difference between ho fast something is downloaded(actual) and how fast your browser and graphics card can render the page and graphics and show them to you.just because you didn’t see it doesn’t mean it didn’t end up in your browser cache.
Tuesday
Scripting Languages
Secure Computer: Scripting Languages
Many scripting languages have been used to develop applications that allow businesses to bring their products or services to the web. This is Great but it also creates a new avenue of attack for hackers.
The majority of web application vulnerabilities come not from bugs int he chosen language but in the methods and procedures used to develop the web application as well as hot the web server was configured.
suppose " if a form requests a zip code and the user enters "ABCDE" ,the application may fail if the developer did not properly validate incoming form data. several languages can be used for creating web applications, including CGI's, PHP and ASP.
- CGI( Common Gateway Interface) : A standard way for a web server to pass a web user's request to an application program and to receive data back to forward to the user. CGI is part of the web's hypertext transfer protocol(HTTP). The most popular CGI application are : C,C++,JAVA and PERL.
- PHP : PHP is an open source server side scripting language where the script is embedded within a web page along with its HTML> before page is sent to a user, the web server calls PHP to interpret and perform any operations called for in the PHP script. whereas HTML displays static content, PHP allows the developer to build pages that present the user with dynamic, customized content based on user input. File name with the suffix "PHP".
- ASP(Active Server Pages) : Web pages that have an .asp active server pages (ASP), are database drive dynamically created web page with a .ASP extension. They utilize ActiveX scripting usually VB Script or Jscript code. When browser requests an ASP, The web server generates a page with HTML code and immediately sends it back to the browser in this way they allow web users to view real time data, but they are more vulnerable to security problems.
Honeypots
In a honeypot, there are no authorized users, no real data is stored in the system, no real work is Performed on it, so every access, every attempt to use it, can be identified as unauthorized. Instead of sifting through logs to identify intrusions, the system administrator knows that every access is an intrusion, so a large part of the work is already done.
Thursday
Touchscreens Type
Wednesday
Protecting Services
Protecting Services
Protecting Services
How Firewall Can Protect Your Computer
- Command-channel attacks
- A firewall can protect against command-channel attacks by restricting the number of machines to which attackers can open command channels and by providing a secured server on those machines. In some cases, it can also filter out clearly dangerous commands (for instance, invalid commands or commands you have decided not to allow).
- Data-driven attacks
- A firewall can't do much about data-driven attacks; the data has to be allowed through, or you won't actually be able to do anything. In some cases, it's possible to filter out bad data. For instance, you can run virus scanners over email and other file transfer protocols. Your best bet, however, is to educate users to the risks they run when they bring files to their machine and when they send data out, and to provide appropriate tools allowing them to protect their computers and data. These include virus checkers and encryption software.
- Third-party attacks
- Third-party attacks can sometimes be prevented by the same sort of tactics used against command-channel attacks: limit the hosts that are accessible to ones where you know only the desired services are available, and/or do protocol checking to make certain that the commands you're getting are for the service you're trying to allow.
- False authentication of clients
- A firewall cannot prevent false authentication of clients. It can, however, limit incoming connections to ones on which you enforce the use of nonreusable passwords.
- Hijacking
- A firewall can rarely do anything about hijacking. Using a virtual private network with encryption will prevent it; so will protocols that use encryption with a shared secret between the client and the server, which will keep the hijacker from being able to send valid packets. Using TCP implementations that have highly unpredictable sequence numbers will decrease the possibility of hijacking TCP connections. It will not protect you from a hijacker that can see the legitimate traffic. Even somewhat unpredictable sequence numbers will help; hijacking attempts will create a burst of invalid packets that may be detectable by a firewall or an intrusion detection system. (Sequence numbers and hijacking are discussed in more detail in Chapter 4, Packets and Protocols.)
- Packet sniffing
- A firewall cannot do anything to prevent packet sniffing. Virtual private networks and encrypted protocols will not prevent packet sniffing, but they will make it less damaging.
- Data injection and modification
- There's very little a firewall can do about data injection or modification. A virtual private network will protect against it, as will a protocol that has message integrity checking.
- Replay
- Once again, a firewall can do very little about replay attacks. In a few cases, where there is literally a replay of exactly the same packet, a stateful packet filter may be able to detect the duplication; however, in many cases, it's perfectly reasonable for that to happen. The primary protection against replay attacks is using a protocol that's not vulnerable to them (one that involves message integrity and includes a timestamp, for instance).
- Denial of service
- Firewalls can help prevent denial of service attacks by filtering out forged or malformed requests before they reach servers. In addition, they can sometimes provide assistance by limiting the resources available to an attacker. For instance, a firewall can limit the rate with which it sends traffic to a server, or control the balance of allowed traffic so that a single source cannot monopolize services.
-
McAfee Total Protection
My choice
If you work more than Hour on net , viewing more and more site , you can use Trend Micro Titanium
For more protection ,
-
AVG antivirus Best in its Competitor
you can use it free for one year
- Source
Monday
Attacks Though Commands
A command channel attack is one that directly attacks a particular service's server by sending
it commands in the same way it regularly receives them(down it command channel).
There are two Types of Command Channel Attacks
1.Attacks that exploit valid commands to do undesirable things
2.Attacks that send invalid commands and exploit server bugs ind dealing with invalid input.
 |
| Command Prompt CMD |
Data Driven Attacks
A data driven attacks is one that involves the data transferred by a protocol, instead of the server
that implements it.
There are two types of data driven attacks
 |
| Blocking The Attacks |
 |
| SSL Connection |
1.Attacks that involve evil data
2.Attacks that compromise good data
Viruses transmitted in electronic mail messages are data driven attacks that involve evil data
Attack that steal credit card numbers in transit are data driven attack that compromise good data
Third Party Attacks
A third-party attack is one that doesn't involve the service you're intending to support at all but that uses the provisions you've made to support one service in order to attack a completely different one. For instance, if you allow inbound TCP connections to any port above 1024 in order to support some protocol, you are opening up a large number of opportunities for third-party attacks as people make inbound connections to completely different servers.
| Stolen Life |
More
Web Application Problems
TCP/IP
Boot Virus



